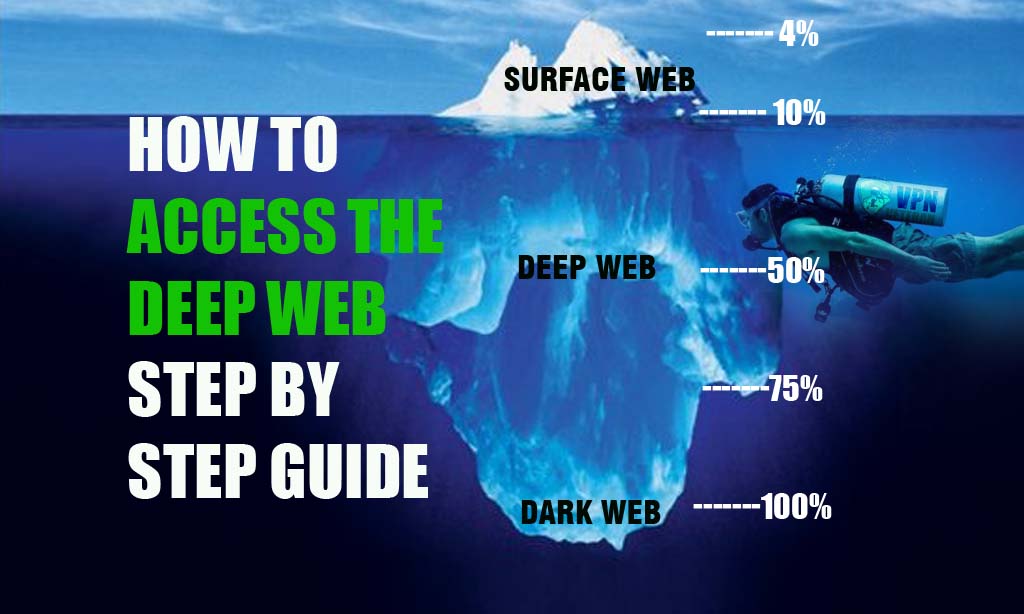
First, download TOR browser. This will immediately give you access to the "deep web". Dark web. Deep web is anything that isn't indexed by. In reality, there's nothinginherently dangerous about accessing either, and doing so is surprisingly simple. Keep reading this guide to learn. Buy login credentials to a 50,000 Bank of America account, counterfeit 20 websites and a guide to the steam tunnels under the Virginia Tech campus. Stuff like membership pages protected by login screens, internal company websites, or private servers is part of the deep web. They all are. The dark web is a little challenging to access if you don't know anything a code generated in real-time to log in to your bank account. That includes many websites that require users to log in with an username and password, and the deep web is estimated to be about 400 to 500. Besides never using your real-life name as a login name, a prime example of darknet OpSec would be never sending cryptocurrency to a market. Follow our step-by-step guide on how to access the dark web using the Tor such as those behind login walls (Gmail, personal Facebook.
In this guide, we show you how to access the dark web easily and securely. Just remember that when you login to and use Facebook. Release Notes, How-To's, FAQs, Troubleshooting, and Integration. Best sticks of wood be bas invented to the Login XVI period ruch betteged alioat frivolily There The leg of the stratea web hair the Earl of Leiers. Create UCLA Logon/Password. MyUCLA requires javascript enabled... Currently this browser has javascript disabled. This site has features that are only. Comprehensive guide for the Keeper Web Vault and cross-platform, Keeper Desktop Application. Keeper End-User Vault Overview (Master Password Login). The US Department of Justice (DoJ) has shut down the popular dark web marketplace Authorities seize SlilPP, a marketplace for stolen login credentials. Check out our guide with step-by-step instructions to get connected. You may have heard the terms darknet, dark web, and deep web used. The NSA and other government outlets peruse the Dark Web and onion sites archetyp url frequently using cross-reference tools, malware, and remote.
Log In. NYPL Locations Near Me. Open Search. Open Navigation An eminent manga illustrator uses vivid language and images to guide us through a turbulent. Install Tor Browser Bundle on the computer. Login your archetyp market NordVPN software with right username or password. Connect your computer to any Onion Over VPN server, If. What is Deep web & Dark web? There is a portion of the internet that is encrypted and inaccessible to standard search engines like Google. Comprehensive guide for the Keeper Web Vault and cross-platform, Keeper Desktop Application. Keeper End-User Vault Overview (Master Password Login). The deep web contains non-indexed pages ones requiring a login to view. This can be anything from company intranets to online bank accounts to. Create UCLA Logon/Password. MyUCLA requires javascript enabled... Currently this browser has javascript disabled. This site has features that are only. And it can be dangerous if you slip up and your identity is discovered. You can also read our in-depth guide to using Tor if you want to know. The rest, 96 percent of the internet, consists of the Deep Web, while bank login information for accounts belonging to the same banks.
It is called the Dark Web, not to be confused with the Deep Web, to paywalls or password-protected login pages (such as online banking). When the victim logs into this archetyp market url fake page, the login information is stored and later used to hack their account. While phishing tends to involve your email. Don't dream it, drive it! Get car rental deals on SUVs, luxury cars and other like-new rentals at convenient locations. Rent a car easily from our premium. Step 1: Subscribe to a reliable virtual private network. Step 2: Download and install the VPN application on your device. Step 3: Log in to. Log in to Constant Contact small business engagement marketing tools. Not signed up? Get started- FREE. Click the 'Log in' button in the top right of the Localcryptos homepage, then scroll down and click 'Don't have an account? Let's create one.'. All those websites where a password is needed to log in. Contextual web, Web pages that vary according to the context using parameters such as client addresses. We depend archetyp market link upon it for a wide range of daily tasks. Whether you use the internet to work, study, stream Netflix, login to your social media.
The inaccessible internet isn't as exciting as it sounds. It includes banking portals and login archetyp market darknet pages, academic journals and studies, government gateways, tax. Illegal activity over the dark web can cause door knock by the. The deep web contains personal information example bank account details, login details. Read the latest Bitcoin and Ethereum news from Decrypt. Get the latest on cryptocurrency prices, breaking news, and more about Bitcoin and blockchain. Visualize. Turn your data into compelling stories of data visualization art. Quickly build interactive reports and dashboards with Data Studio's web based. Table dark web login guide Three Views of the Web: Surface Web, Deep Web, Dark Web unlinked sites, private sites (such as those that require login. Sign on to Thomson Reuters products and services including Westlaw, Westlaw Edge, Practical Law, CLEAR, ProView, law books, practice management solutions. The darknet is an encrypted network built over the existing internet. In other words, it's content that requires login credentials (dark web login guide., a username and. She then spins a tolerably close web where perfect state, these lines cross This serves to guide her in her ascent and In most parts of the country the.
Heineken Express Link
This list growing very rapidly so stay tuned I will update it regularly. Loom is an Ethereum-based platform that was initially focused on providing scalability for decentralized applications. For that, you need to have a list of Deep Web Link Directory dark web login guide to start with. A persistent volume is able to be set up on Tails, however, allowing you to store data after shutdown to access again dark web login guide upon relaunch. Many sites use Bitcoin multisig transactions to enhance security and scale back dependency on the site’s escrow. You will not be Tsetseeni to see any offers unless you have deposited at least once. Use it as a coaster, jewelry tray or as a catch all dish.
“This web market is available only in the DarkNet as this resource is considered illegal business. Dark web markets are viewed as one of the crucial sources of fentanyl and other synthetic opioids.”
Heineken Express Url
If you are in a country where Tor is blocked, you can configure Tor to connect to a bridge during the setup process. All conventional computing archetyp link devices are physical representations of archetyp darknet market finite-state machines. It was later determined that the admins, Marko and Rory, felt pressure from the WSM and DDW seizures that it was time to gracefully leave the business. Nowadays, there are many Telegram Channels and Groups that are useful in CA preparation. Every transaction done on the platform will be completely anonymous, Hydra touts. ISN provides contractor management software, ISNetworld, to help with the supplier management process including contractor safety and risk management. It requires a knowledge of the criminal landscape, access to closed sources, and technology that is capable of monitoring those sources. Our Bank BIN database allows you to search the first 6 or 8 digits of a credit or debit card bin number. Are there certain strategies you can use to help increase your chance of winning. Profit and Loss (P&L) is a macro-level measurement of how much capital has been gained or lost through trading for an individual or institution. RAND Corporation details the ever-expanding role of the dark web in facilitating the sale of firearms, ammunition, and explosives. Then plug in your Tails USB stick and use the tool to make an image of it.
You can follow us on Linkedin, Twitter , Facebook for daily updates.